Open the macOS High Sierra Patcher tool, navigate to the High Sierra Installer App, then select your pen drive and click “Start Operation”. Boot from the USB drive by holding down the option key after reboot. Install macOS normally, reboot back on the installer drive, and then open the “macOS Post Install” application. Overview macOS High Sierra Patcher, the successor to macOS Sierra Patcher, is an easy-to-use tool that allows anyone to install macOS High Sierra on unsupported Macs. What's new in macOS High Sierra Patcher Version 2.7.0.
I also have a YouTube video going over the whole process.
Requirements:
- Early-2008 or newer Mac Pro, iMac, or MacBook Pro(MacPro 3,1 and 4,1, iMac 8,1 and 9,1, MacBook Pro 4,1, 5,1 5,2, 5,3,5,4, and 5,5)
- Late-2008 or newer MacBook Air or Aluminum Unibody MacBook (MacBookAir 2,1, MacBook 5,1)
- Early-2009 or newer Mac Mini or white MacBook (Macmini 3,1, MacBook 5,2)
- Early-2008 or newer Xserve (Xserve 2,1, Xserve 3,1)
Machines that ARE NOT supported:
- 2006-2007 Mac Pros, iMacs, MacBookPros, and Mac Minis (MacPro 1,1 and 2,1, iMac 4,1, 5,1, 5,2, 6,1 and7,1, MacBook Pro 1,1, 2,1, and 3,1, Macmini 1,1 and 2,1)
-- The 2007 iMac 7,1 is compatible if the CPU is upgraded to a Penryn-based Core 2 Duo, such as a T9300.
- 2006-2008 MacBooks (MacBook 1,1, 2,1 3,1 and 4,1)
- 2008 MacBook Air (MacBookAir 1,1)
-- Note: Make sure SIP is disabled on the system you intend to installHigh Sierra on. If it's not or you're unsure, just boot into your Recoverypartition of your currently installed copy of OS X, open Terminal, andrun 'csrutil disable'.
Things you'll need:
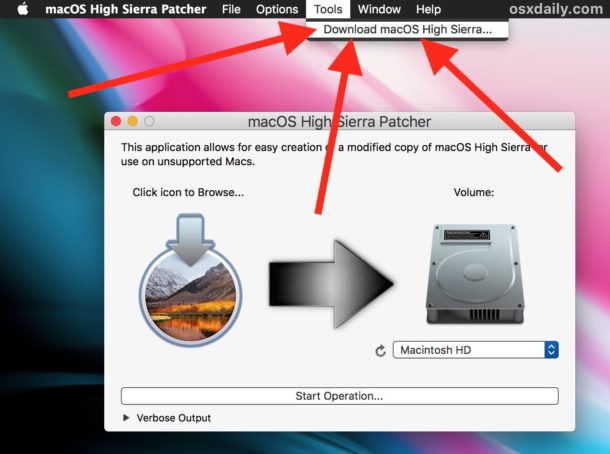
- A copy of the macOS High Sierra InstallerApp. This can be obtained from the Mac App Store using a machinethatsupports High Sierra, or by using the built-in downloading feature of the tool. In the Menu Bar, simply select 'Tools > Download macOS High Sierra...'
- A USB drive that's at least 8 GB in size
- A copy of the tool - Download here (Current version: 2.7.0, SHA1: 73f180d30200ef5f6d900440fe57b9c7d22bd6bf)
-- View changelog and download older versions here
Known issues:
- Trackpad (MacBook5,2 affected only). The trackpad in the MacBook5,2isn't fully supported in High Sierra. While it works and is fully usable,High Sierra detects it as just a standard mouse, preventing you fromchanging some trackpad-oriented settings.
How to use:
1. Insert your desired USB drive, open Disk Utility, and format it as OS X Extended (Journaled).
2. Open the 'macOS High Sierra Patcher' tool, and browse for your copy of the macOS High Sierra Installer App.
*Ensure that the tool successfully verifies the app.
3. Next, select your USB drive in the Target Volume list, and click 'Start Operation.'
4. When the operation completes, boot your target unsupported Mac offthe USB drive you just created by holding down the Option key while turning on the machine, and selecting the drive.
Note: Only perform steps 5 and 6 if you intend to do a clean install.Otherwise, you can simply skip these steps and install to your volumecontaing a previous version of OS X, and it'll do an in-place upgrade.
5. When the installer boots, open Disk Utility from the Utilities menu, or by double-clicking it in the Utilities window on the bottom left corner of the screen.
6. Select the disk or partition you want to install on, and erase it,ensuring to use either Mac OS Extended (Journaled), or APFS as the filesystem type.If formatting an entire drive, ensure GUID is selected.
-- Please note that if you use APFS, you will not have a bootable Recovery partition.
-- It is recommended that you only use APFS if the target drive is an SSD.
-- If you decide to use APFS, a custom booting method will be installed by the post-install tool, as the firmware of these unsupported machines does not natively support booting from APFS volumes. It is not quite as clean as native booting, but will not cause any issues while running High Sierra. A demo of the modified booting process can be viewed here.
7. Install macOS normally onto the desired volume.
8. When the install completes, reboot back onto the installer drive.This time, open the 'macOS Post Install' application.
9. In the application, select the Mac model you are using. The optimalpatches will be selected for you based on the model you select. You canalso select other patches of your choosing.
-- The 'i' button next to each patch will show more details about the respective patch.
10. Select the volume you have just installed macOS High Sierra on, andclick 'Patch.' When it finishes patching, click 'Reboot'. It may sitthere for a few moments rebuilding caches before rebooting.
-- If for somereason the system fails to work correctly after rebooting, boot backinto your installer drive, run the post install patch again, and select'Force Cache Rebuild' before rebooting. This isn't necessary under mostcircumstances.
11. When it reboots, it should now boot into a fully working copy ofmacOS High Sierra.
Additional Info:
- If selected in the macOS Post Install tool, your High Sierra install will have a program named 'Patch Updater' located in your /Applications/Utilities folder. This program will alert you when new updates to patches are available for your machine, and will prompt you to install them. If you do not have Patch Updater installed, but would like it, you can download and run the script found here to do so.
Updates
System updates, such as 10.13.1, should install normally if 'Software Update Patch' was selected in the macOS Post Install tool, or installed using the Patch Updater program. If for some reason updates aren't showing up, or you did not apply the patch, you can install it manually using the script found here.
-- If the machine does not start up properly after applying a system update, you will need to boot off your patched installer volume, and re-run the post-install patch on your High Sierra volume. Ensure you select 'Force Cache Rebuild' before rebooting.
FAQ:
Q: The tool created the USB drive successfully, but when booting, the progress bar hangs a bit more than half way.
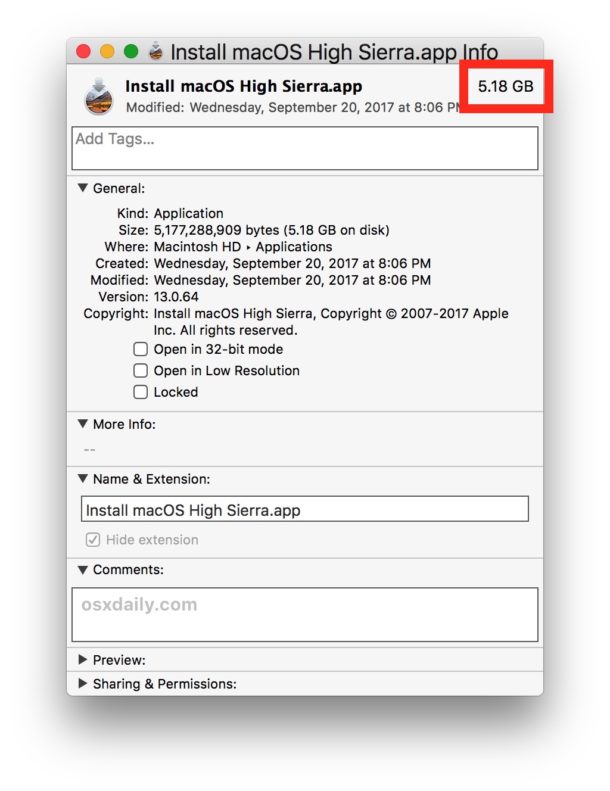
A: Check your copy of the Install macOS High Sierra App. If you're using thelatest version of the tool, you must be using the latest version of theInstall macOS High Sierra App. Version 1.1 ofthe patch tool and older support older versions of the installer app.
Q: The patch tool gives me errors, such as 'Error copying files...'.
A: Check to make sure your USB drive is writeable. Try re-formatting it, or just try a different USB drive.
Q: The patch tool gives me a 'Mounting Failed' error
A: Check to make sure your Install macOS High Sierra App is the correct one.It should be around 5GB in size. If you used the 'Skip AppVerification' option, you have most likely selected an invalid app thatdoesn't contain the necessary files.
Q: I cannot open my copy of Install macOS High Sierra with the patch tool.
A: If you downloaded the copy linked above, it is distributed inside aDMG file. You must open this file (mount it) to access the InstallmacOS High Sierra App you need to select.
Q: I don't see my hard drive partition in the installer screen or in the post-install tool.
A: Make sure FileVault is disabled, or use the instructions found here to unlock it manually using Terminal.
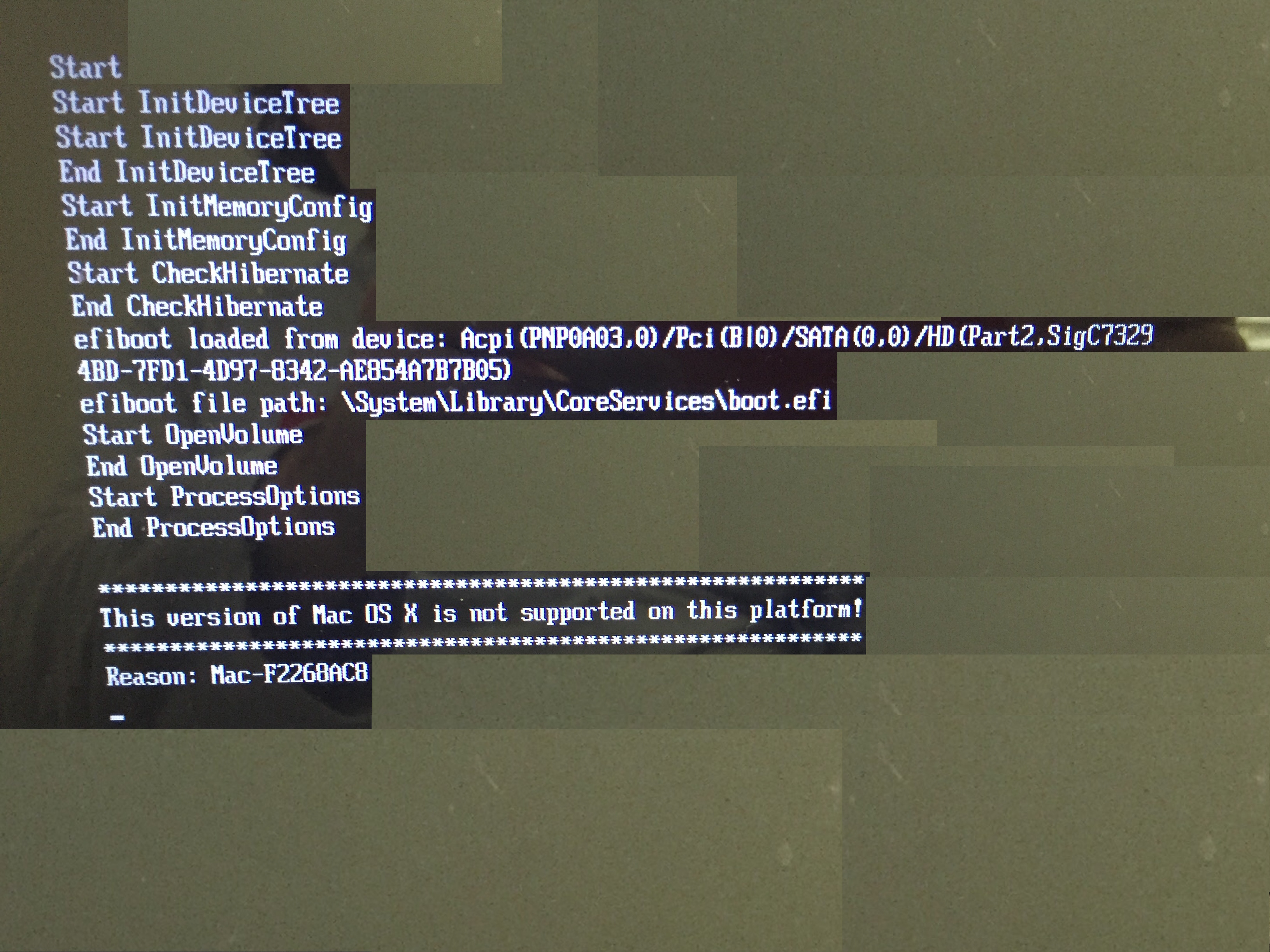
Q: I get a 'NO' symbol when starting up after successfully installing High Sierra.
A: Make sure you have run the post-install patch on the correct volume, as detailed above in steps 8-10.
Q: I get a 'NO' symbol when starting up from the patched USB drive
A: Check the supported/not supported list at the top of this page. Ensure your machine is in the supported list.
Q: My iSight camera doesn't work after installing High Sierra
A: Make sure you properly remove (using the program's uninstaller, not by simply dragging the application to the Trash) all virtual machine software installed on your machine, such as VirtualBox, VMWare, etc.
Q: I get 'NSURL' errors when trying to update my machine or use the App Store
A: This is usually the result of having an invalid CatalogURL set. To revert to stock, simply run 'sudo softwareupdate --clear-catalog' in Terminal, and then run the software update patch script located above.
Q: Safari, App Store, and/or Mail stopped working after installing a system update
A: Download and run the Onyx application, select 'Maintenence' at the top, then click the Run button.
Q: I get a 'No packages were eligible for install' error when attepting to install High Sierra
A: This is due to your system's date and time being set incorrectly. To fix it, you can either boot into your current OS X install and set the date, or you can use Terminal after booting from your patched USB installer drive to set the date. Instructions to set the date using Terminal can be found here.
About Apple security updates
For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available. Recent releases are listed on the Apple security updates page.
Apple security documents reference vulnerabilities by CVE-ID when possible.
For more information about security, see the Apple Product Security page.
macOS Mojave 10.14.5, Security Update 2019-003 High Sierra, Security Update 2019-003 Sierra
Released May 13, 2019
Accessibility Framework
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.4
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2019-8603: Phoenhex and qwerty (@_niklasb, @qwertyoruiopz, @bkth_) working with Trend Micro's Zero Day Initiative
AMD
Available for: macOS Mojave 10.14.4
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8635: Lilang Wu and Moony Li of TrendMicro Mobile Security Research Team working with Trend Micro's Zero Day Initiative
Application Firewall
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.4
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A logic issue was addressed with improved restrictions.
CVE-2019-8590: The UK’s National Cyber Security Centre (NCSC)
Archive Utility
Available for: macOS Mojave 10.14.4
Impact: A sandboxed process may be able to circumvent sandbox restrictions
Description: A logic issue was addressed with improved validation.
CVE-2019-8640: Ash Fox of Fitbit Product Security
Entry added August 1, 2019
Bluetooth
Available for: macOS Mojave 10.14.4
Impact: Due to a misconfiguration in the Bluetooth pairing protocols of a Bluetooth Low Energy (BLE) version of FIDO Security Keys it may be possible for an attacker with physical proximity to be able to intercept Bluetooth traffic during pairing
Description: This issue was addressed by disabling accessories with insecure Bluetooth connections. Customers using the Bluetooth Low Energy (BLE) version of the Titan Security Key by Google should review Android’s June Bulletins and Google’s advisory and take appropriate action.
CVE-2019-2102: Matt Beaver and Erik Peterson of Microsoft Corp.
Entry added September 17, 2019
CoreAudio
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.4, macOS High Sierra 10.13.6
Impact: Processing a maliciously crafted audio file may lead to arbitrary code execution
Description: A memory corruption issue was addressed with improved error handling.
CVE-2019-8592: riusksk of VulWar Corp working with Trend Micro's Zero Day Initiative
Entry updated October 8, 2019
CoreAudio
Available for: macOS Mojave 10.14.4
Impact: Processing a maliciously crafted movie file may lead to arbitrary code execution
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2019-8585: riusksk of VulWar Corp working with Trend Micro's Zero Day Initiative
CoreText
Available for: macOS Mojave 10.14.4
Impact: Processing a maliciously crafted font may result in the disclosure of process memory
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2019-8582: riusksk of VulWar Corp working with Trend Micro's Zero Day Initiative
Entry added July 25, 2019
DesktopServices
Available for: macOS Mojave 10.14.4
Impact: A malicious application may bypass Gatekeeper checks
Description: This issue was addressed with improved checks.
CVE-2019-8589: Andreas Clementi, Stefan Haselwanter, and Peter Stelzhammer of AV-Comparatives
Disk Images
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.4, macOS High Sierra 10.13.6
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2019-8560: Nikita Pupyshev of Bauman Moscow State Technological University
Entry updated May 14, 2019
EFI
Available for: macOS Mojave 10.14.4
Impact: A user may be unexpectedly logged in to another user’s account
Description: An authentication issue was addressed with improved state management.
CVE-2019-8634: Jenny Sprenger and Maik Hoepfel
Intel Graphics Driver
Available for: macOS Mojave 10.14.4
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8616: Lilang Wu and Moony Li of Trend Micro Mobile Security Research Team working with Trend Micro's Zero Day Initiative
Intel Graphics Driver
Available for: macOS High Sierra 10.13.6, macOS Mojave 10.14.4
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2019-8629: Arash Tohidi of Solita Oy
IOAcceleratorFamily
Available for: macOS High Sierra 10.13.6
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2018-4456: Tyler Bohan of Cisco Talos
IOKit
Available for: macOS High Sierra 10.13.6, macOS Mojave 10.14.4
Impact: A local user may be able to load unsigned kernel extensions
Description: A validation issue existed in the handling of symlinks. This issue was addressed with improved validation of symlinks.
CVE-2019-8606: Phoenhex and qwerty (@_niklasb, @qwertyoruiopz, @bkth_) working with Trend Micro's Zero Day Initiative
Kernel
Available for: macOS Mojave 10.14.4, macOS High Sierra 10.13.6
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2019-8633: Zhuo Liang of Qihoo 360 Vulcan Team
Entry added July 25, 2019, updated September 17, 2019
Kernel
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed with improved state management.
CVE-2019-8525: Zhuo Liang and shrek_wzw of Qihoo 360 Nirvan Team
Entry added May 14, 2019
Kernel
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6
Impact: A remote attacker may be able to leak memory
Description: An out-of-bounds read issue existed that led to the disclosure of kernel memory. This was addressed with improved input validation.
CVE-2019-8547: derrek (@derrekr6)
Entry added May 14, 2019
Kernel
Available for: macOS Mojave 10.14.4
Impact: A local user may be able to cause unexpected system termination or read kernel memory
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2019-8576: Brandon Azad of Google Project Zero, Junho Jang and Hanul Choi of LINE Security Team
Entry updated May 30, 2019
Kernel
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.4
Impact: An application may be able to cause unexpected system termination or write kernel memory
Description: A type confusion issue was addressed with improved memory handling.
CVE-2019-8591: Ned Williamson working with Google Project Zero
Messages
Available for: macOS Mojave 10.14.4
Impact: A remote attacker may be able to cause a system denial of service
Description: An input validation issue was addressed with improved input validation.
CVE-2019-8573: Natalie Silvanovich of Google Project Zero
Entry added July 3, 2019
Messages
Available for: macOS Mojave 10.14.4
Impact: Users removed from an iMessage conversation may still be able to alter state
Description: A logic issue was addressed with improved state management.
CVE-2019-8631: Jamie Bishop of Dynastic
Entry added August 1, 2019
Microcode
Available for: macOS Mojave 10.14.4
Impact: Load ports, fill buffers, and store buffers in systems with microprocessors utilizing speculative execution may allow an attacker with local user access to potentially enable information disclosure via a side channel
Description: Multiple information disclosure issues were addressed partially by updating the microcode and changing the OS scheduler to isolate the system from web content running in the browser. To completely address these issues, there are additional opt-in mitigations to disable hyper threading and enable microcode-based mitigations for all processes by default. Details of the mitigations can be found at https://support.apple.com/kb/HT210107.
CVE-2018-12126: Ke Sun, Henrique Kawakami, Kekai Hu, and Rodrigo Branco from Intel; Lei Shi - Qihoo 360 CERT; Marina Minkin; Daniel Genkin from University of Michigan; and Yuval Yarom from University of Adelaide
CVE-2018-12127: Brandon Falk from Microsoft Windows Platform Security Team; and Ke Sun, Henrique Kawakami, Kekai Hu, and Rodrigo Branco from Intel
CVE-2018-12130: Giorgi Maisuradze from Microsoft Research; Ke Sun, Henrique Kawakami, Kekai Hu, and Rodrigo Branco from Intel; Moritz Lipp, Michael Schwarz, and Daniel Gruss from Graz University of Technology; Stephan van Schaik, Alyssa Milburn, Sebastian Osterlund, Pietro Frigo, Kaveh Razavi, Herbert Bos, and Cristiano Giuffrida from VUSec group at VU Amsterdam; Volodymyr Pikhur; and Dan Horea Lutas from BitDefender
CVE-2019-11091: Ke Sun, Henrique Kawakami, Kekai Hu, and Rodrigo Branco from Intel; and Moritz Lipp, Michael Schwarz, and Daniel Gruss from Graz University of Technology
Entry added May 14, 2019
Security
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.4
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8604: Fluoroacetate working with Trend Micro's Zero Day Initiative
SQLite
Available for: macOS Mojave 10.14.4
Impact: An application may be able to gain elevated privileges
Description: An input validation issue was addressed with improved memory handling.
CVE-2019-8577: Omer Gull of Checkpoint Research
SQLite
Available for: macOS Mojave 10.14.4
Impact: A maliciously crafted SQL query may lead to arbitrary code execution
Description: A memory corruption issue was addressed with improved input validation.
CVE-2019-8600: Omer Gull of Checkpoint Research
SQLite
Available for: macOS Mojave 10.14.4
Impact: A malicious application may be able to read restricted memory
Description: An input validation issue was addressed with improved input validation.
CVE-2019-8598: Omer Gull of Checkpoint Research
SQLite
Available for: macOS Mojave 10.14.4
Impact: A malicious application may be able to elevate privileges
Description: A memory corruption issue was addressed by removing the vulnerable code.
CVE-2019-8602: Omer Gull of Checkpoint Research
StreamingZip
Available for: macOS Mojave 10.14.4
Impact: A local user may be able to modify protected parts of the file system
High Sierra Patcher
Description: A validation issue existed in the handling of symlinks. This issue was addressed with improved validation of symlinks.
CVE-2019-8568: Dany Lisiansky (@DanyL931)
sysdiagnose
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.4
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8574: Dayton Pidhirney (@_watbulb) of Seekintoo (@seekintoo)
Touch Bar Support
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8569: Viktor Oreshkin (@stek29)
WebKit
Available for: macOS Mojave 10.14.4
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: Multiple memory corruption issues were addressed with improved memory handling.
CVE-2019-6237: G. Geshev working with Trend Micro Zero Day Initiative, Liu Long of Qihoo 360 Vulcan Team
CVE-2019-8571: 01 working with Trend Micro's Zero Day Initiative
CVE-2019-8583: sakura of Tencent Xuanwu Lab, jessica (@babyjess1ca_) of Tencent Keen Lab, and dwfault working at ADLab of Venustech
CVE-2019-8584: G. Geshev of MWR Labs working with Trend Micro Zero Day Initiative
CVE-2019-8586: an anonymous researcher
CVE-2019-8587: G. Geshev working with Trend Micro Zero Day Initiative
CVE-2019-8594: Suyoung Lee and Sooel Son of KAIST Web Security & Privacy Lab and HyungSeok Han and Sang Kil Cha of KAIST SoftSec Lab
CVE-2019-8595: G. Geshev from MWR Labs working with Trend Micro Zero Day Initiative
CVE-2019-8596: Wen Xu of SSLab at Georgia Tech
CVE-2019-8597: 01 working with Trend Micro Zero Day Initiative
CVE-2019-8601: Fluoroacetate working with Trend Micro's Zero Day Initiative
CVE-2019-8608: G. Geshev working with Trend Micro Zero Day Initiative
CVE-2019-8609: Wen Xu of SSLab, Georgia Tech
CVE-2019-8610: Anonymous working with Trend Micro Zero Day Initiative
CVE-2019-8611: Samuel Groß of Google Project Zero
CVE-2019-8615: G. Geshev from MWR Labs working with Trend Micro's Zero Day Initiative
CVE-2019-8619: Wen Xu of SSLab at Georgia Tech and Hanqing Zhao of Chaitin Security Research Lab
CVE-2019-8622: Samuel Groß of Google Project Zero
CVE-2019-8623: Samuel Groß of Google Project Zero
High Sierra Patcher Tool
CVE-2019-8628: Wen Xu of SSLab at Georgia Tech and Hanqing Zhao of Chaitin Security Research Lab
WebKit
Available for: macOS Mojave 10.14.4
Impact: Processing maliciously crafted web content may result in the disclosure of process memory
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2019-8607: Junho Jang and Hanul Choi of LINE Security Team
Wi-Fi
Available for: macOS Mojave 10.14.4
Impact: An attacker in a privileged network position can modify driver state
High Sierra Patcher Tool
Description: A logic issue was addressed with improved state management.
CVE-2019-8612: Milan Stute of Secure Mobile Networking Lab at Technische Universität Darmstadt
Entry added May 14, 2019
Additional recognition
CoreAudio
We would like to acknowledge riusksk of VulWar Corp working with Trend Micro's Zero Day Initiative for their assistance.
Entry added July 25, 2019
CoreFoundation
We would like to acknowledge m4bln, Xiangqian Zhang, Huiming Liu of Tencent's Xuanwu Lab, Vozzie, and Rami for their assistance.
Entry updated May 14, 2019
Kernel
We would like to acknowledge Denis Kopyrin for their assistance.
Entry updated May 14, 2019
PackageKit
We would like to acknowledge Csaba Fitzl (@theevilbit) for their assistance.
Safari
We would like to acknowledge Michael Ball of Gradescope by Turnitin for their assistance.
System Preferences
Dosdude Patcher
We would like to acknowledge an anonymous researcher for their assistance.
